
STIR/SHAKEN Compliance for Call Centers: What You Need to Know
What is STIR/SHAKEN?
STIR/SHAKEN is a technology framework that helps phone carriers verify whether a call is really coming from the number it claims to.
The name isn’t intuitive, so here’s the breakdown:
STIR: Secure Telephone Identity Revisited
SHAKEN: Signature-based Handling of Asserted Information Using toKENs
This framework was introduced to tackle the surge of scam calls and spoofed caller IDs that frustrate both consumers and businesses. To address the issue, Congress passed the TRACED Act, giving the FCC authority to require STIR/SHAKEN implementation. It became mandatory for voice service providers on IP networks by June 30, 2021.
According to the FCC:
“Widespread deployment of caller ID authentication will reduce the effectiveness of illegal spoofed caller ID, allow law enforcement to identify bad actors more easily, and better enable phone companies to block illegal calls before those calls reach consumers.”
How STIR/SHAKEN works
Here’s the process, simplified:
The originating carrier “signs” the caller ID to confirm the number belongs to the caller.
As the call travels through networks, other carriers check that digital signature.
The recipient’s phone company verifies the caller ID before the call reaches the consumer.
In short: it’s a digital handshake that ensures the number you see is the number that’s really calling.
Currently, STIR/SHAKEN only works on IP-based networks, but the FCC is moving to close loopholes in non-IP networks. Providers will soon be required to certify how they handle caller ID authentication, with two years to comply once the rule takes effect.
FCC enforcement and robocall mitigation
The FCC uses the Robocall Mitigation Database (RMD) to track compliance. Voice service providers must document their robocall mitigation efforts here.
In August 2025, the FCC removed 1,200+ providers from the RMD for failing to comply, banning them from U.S. networks.
FCC Commissioner Brendan Carr said non-compliant providers “have no place in our networks.”
Former Acting Chairwoman Jessica Rosenworcel had previously remarked on FCC priorities:“Protecting consumers from scammers that use robocall and spoofing tools is a top priority… Our message to providers is clear: certify under penalty of perjury the steps you are taking to stop illegal robocalls, or we will block your calls.”
The enforcement efforts are working — consumer robocall complaints have dropped by more than half since 2021.
Why caller ID authentication matters
Caller ID authentication is the process of verifying that the phone number shown on your screen truly matches the source of the call.
This verification matters because it:
Restores consumer trust by reducing spoofed and fraudulent calls.
Improves answer rates — people are more likely to pick up if they believe the call is legitimate.
Supports compliance with FCC rules, protecting your call center from blocks and penalties.
For outbound call centers, caller ID authentication is no longer optional. It’s the difference between leads answering your calls — or never seeing them at all.
What STIR/SHAKEN can and can’t do
✅ What it can do
Authenticate caller identities and reduce spoofing
Help trace illegal calls to their source
Improve consumer protection with a verified caller ID
❌ What it can’t do
Judge whether a call is legal or illegal
Authenticate calls from legacy non-IP networks
Stop all unwanted calls automatically
STIR/SHAKEN compliance for call centers
Even though STIR/SHAKEN is implemented by carriers, call centers still play a critical role in compliance.
What Carriers Handle
Signing outbound calls with a digital token
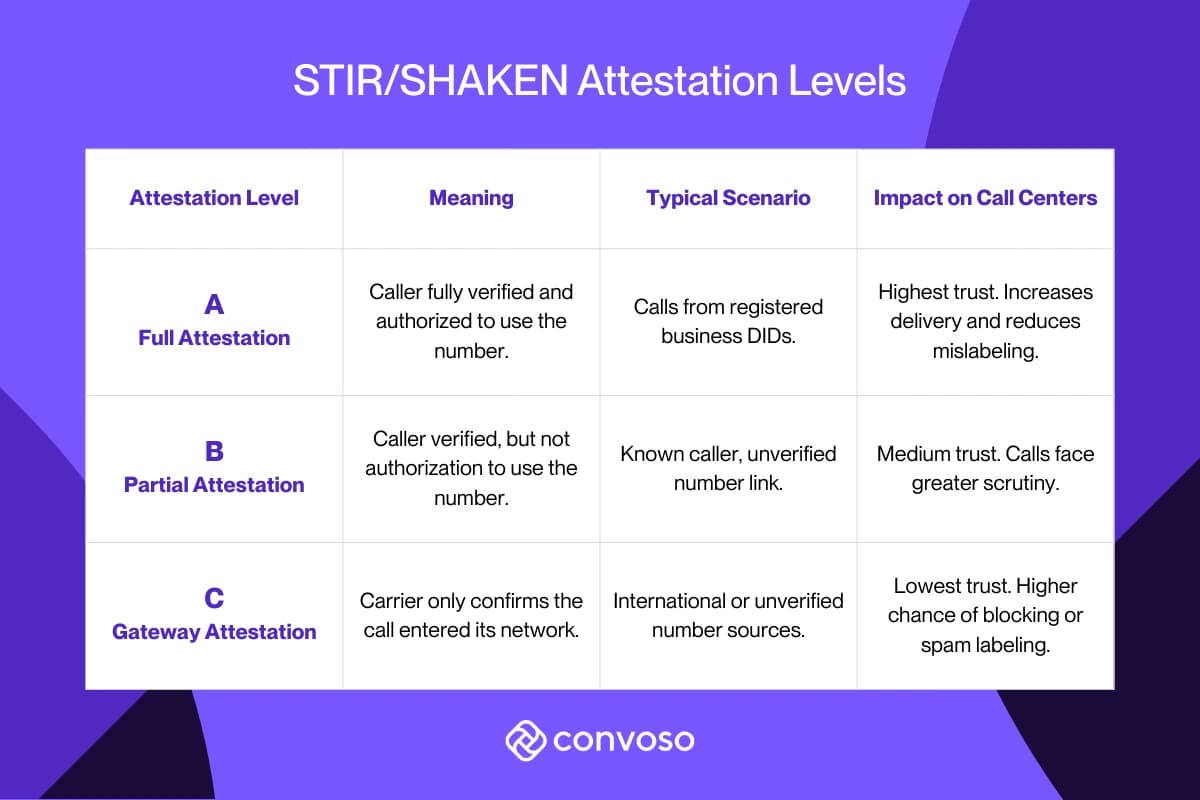
Assigning attestation levels (A, B, C)
Submitting compliance to the Robocall Mitigation Database
Returning SIP 603+ codes for blocked calls
Blocking calls on Do-Not-Originate (DNO) lists
Call center compliance checklist
To improve call delivery and protect your reputation:
Use registered, trusted numbers.
Buy DIDs from reputable carriers and ensure they’re linked to your business.
Maintain responsible call patterns
Avoid spam-like behaviors such as rapid-fire dialing and excessive volumes in short periods.
Choose a compliance-ready dialer platform
While no dialer can guarantee A-level attestation every time, a compliance-focused platform dramatically improves call success.
Know your provider’s status
If your provider uses non-IP networks, they must file a robocall mitigation plan. Verify this or risk having your calls blocked. The FCC began a major crackdown in 2025 for non-compliance with robocall protections
How Convoso helps call centers with STIR/SHAKEN
Convoso is a compliance-focused dialer platform and follows industry best practices. Therefore we are able to sign our calls with the highest level of attestation under the STIR/SHAKEN framework, so that our customers' calls can be transmitted with the strongest security and verification available.
Convoso’s built-in compliance tools support TCPA and state rules, as well as DNC and RND scrubbing. Convoso is also a member of R.E.A.C.H. and the CEO, Nima Hakimi, sits on the board.
But we go further to support compliant-minded businesses. Convoso Ignite is built into the Convoso platform to:
Proactively score DID health on a spectrum based on live performance, not just a reactive “clean/flagged” status.
Automate management of the entire DID lifecycle.
Optimize every call in real time by selecting the best performing number.
Talk to one of our experts to learn how Convoso helps call centers manage compliance while improving contact rates and revenue.
STIR/SHAKEN FAQ’s for call centers
What happens if my call center isn’t STIR/SHAKEN compliant?
Your calls may be blocked before reaching consumers. Non-compliant providers risk removal from U.S. networks.
Does STIR/SHAKEN guarantee my calls will be answered?
No. It validates caller ID but doesn’t guarantee consumer behavior or prevent labeling if patterns resemble spam.
Can STIR/SHAKEN stop all robocalls?
No. It prevents spoofing but can’t block all unwanted calls.
How do attestation levels affect delivery?
Higher attestation = greater trust and fewer blocked/mislabeled calls.
What if my provider uses non-IP networks?
They must file a robocall mitigation plan with the FCC. It’s on you to ensure compliance.
How can I improve my attestation level?
Use verified numbers, follow clean dialing practices, and work with a compliance-first dialer.
Glossary of key terms
STIR (Secure Telephone Identity Revisited): Protocol verifying caller ID.
SHAKEN (Signature-based Handling of Asserted Information Using toKENs): Framework applying STIR in real-world networks.
TRACED Act: 2019 law mandating FCC robocall rules.
Robocall Mitigation Database (RMD): Public FCC database for provider compliance.
Attestation Levels (A, B, C): Ratings showing how certain carriers are about caller ID authenticity.
SIP 603+ Code: Network signal returned when calls are blocked for reputation, not technical failure.
Do-Not-Originate (DNO) List: Numbers never authorized for outbound calls.
Schedule a demo
Supercharge your sales with our AI-powered contact center platform.
